What we implement
- Environment-scoped AI runtime design
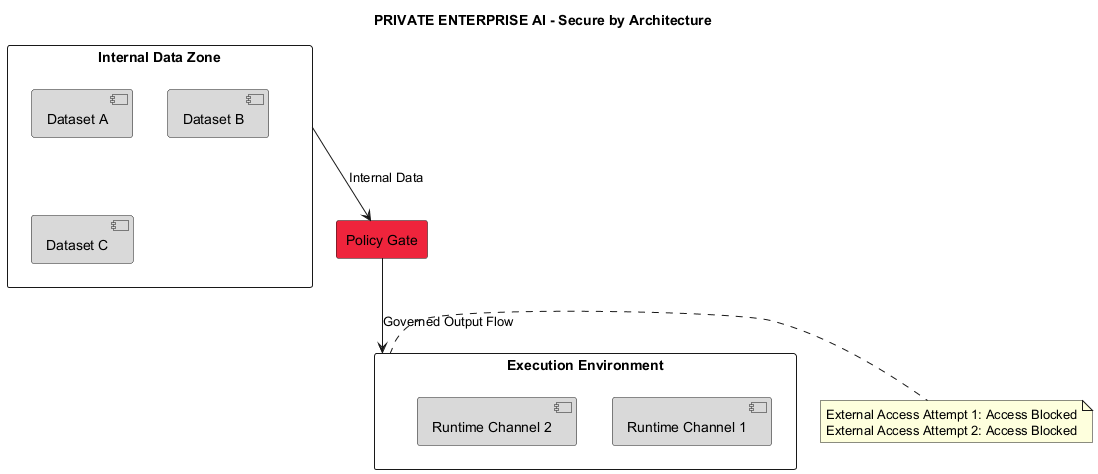
- Data boundary and egress control architecture
- Identity and access integration patterns
- Policy-aligned retrieval and inference design
- Deployment patterns for private cloud and controlled infrastructure